HyperSphere
SecureStorage™
This is what encryption was meant to be: No keys to manage or steal. Security that outsmarts AI and quantum threats. Data protection that just works.
Warning: This is not a better KMS.
HyperSphere SecureStorage™ is a powerful encryption engine that protects unstructured data at rest in S3-compatible object storage without relying on stored keys or external key management systems (KMS).
No Keys to Manage, Lose, or Steal
By definition, encryption and decryption require the use of keys. But SecureStorage uses ephemeral keys. They are derived dynamically, exist only in memory, and are erased when no longer needed. They are never stored or transmitted. No keys persist to be mismanaged or stolen. An entire attack surface disappears.
Quantum Resistance Today
SecureStorage doesn't rely on the type of encryption that quantum computers are expected to break. Our unique methodology uses NIST-approved, quantum-resistant algorithms (AES-256-GCM and KMAC-256) to secure data for decades to come. This isn't a roadmap promise — it's how the product works today.
Seamless Operation
SecureStorage deploys within hours from the AWS Marketplace in cloud, on-prem, or edge environments. The operational burden and risk of key management vanish — nothing to distract your teams, nothing to slow down or break your systems. Users store and access data as they always have. Data protection just happens.
This Is Zero-Management Encryption.
Ephemeral Keying
SecureStorage eliminates persistent, usable key material. Encryption keys are never stored on disk, in databases, or in any external key management service. They exist only during encryption/decryption and are securely erased from memory immediately after use — a lifetime measured in microseconds.
Frame-Level Encryption
HyperSphere's patented encryption methodology is intentionally complex and layered. Data is split into frames, which are then encrypted with AES-256-GCM and distributed across multiple S3-compatible storage backends. Storage operators cannot infer file structures, names, or relationships.
Denial of Access, Never Exposure
SecureStorage is designed to "fail closed." Unauthorized decryption isn't a policy failure waiting to happen — it's architecturally prevented. Accidentally overpermissioned users and intentionally stolen keys can't bypass what's mathematically enforced. A breach yields only partial ciphertext.
S3-Compatible Gateway
SecureStorage uses a standard S3 API. It deploys from the AWS Marketplace and drops in between applications and any S3-compatible object storage. Works with existing apps, SDKs, and CLI tools — no code changes required.
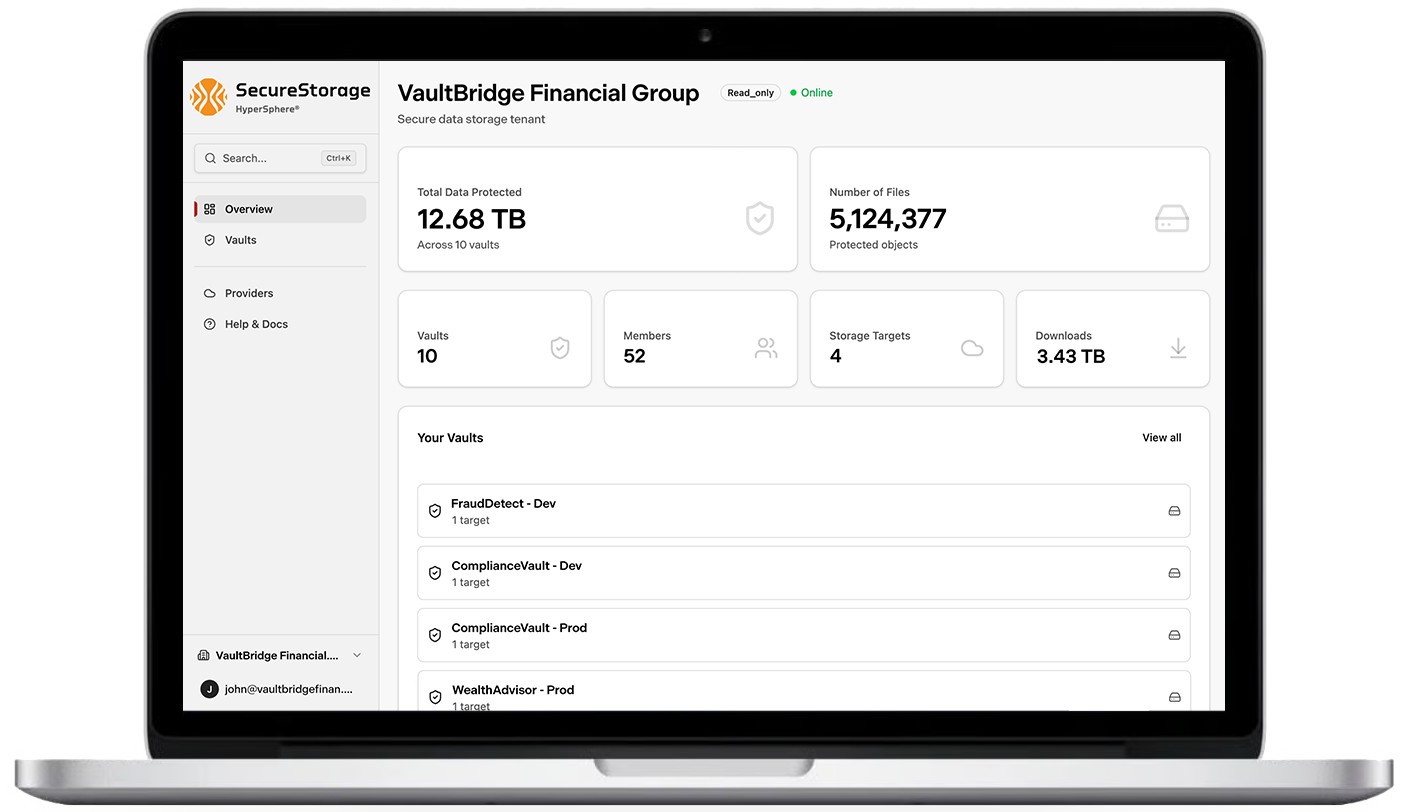
Hybrid Cloud, Single Experience
Protect data across cloud and on-prem environments simultaneously. Distribute protection across regions, providers, and jurisdictions without managing a separate KMS for each.
Audit-Ready from Day One
Every access attempt and operation is logged automatically. Supports compliance with encryption mandates across industries, such as PCI DSS, HIPAA, GDPR, and ITAR/EAR.
Quantum-Safe Protection Without a Migration Project
The standard response to the quantum threat is a multi-year Post-Quantum Cryptography (PQC) migration — new algorithms, new key hierarchies, new integration testing, new risk windows. Every month of inaction is another month of quantum-vulnerable key wrapping and "harvest now, decrypt later" exposure.
SecureStorage sidesteps the entire problem. Because no public-key cryptography exists in the data protection path, there is nothing to migrate. Protection is quantum-resistant from day one — architecturally, not just algorithmically.
Talk to an EngineerReady to Eliminate Key Management?
Deploy SecureStorage™ in hours and eliminate your KMS attack surface entirely.