Data security that works
when everything else fails.
S3 credentials compromised? No problem. With HyperSphere, attackers walk away with unusable data.
Unbreachable is a myth.
We make stolen data useless.
Encrypted data is worthless without the decryption key. Attackers know that, so keys became the target. That's always been a problem. Now, with AI and quantum computing, it's an urgent problem. HyperSphere solves it.
Production-ready in hours. Anywhere.

HyperSphere drops in between applications and S3-compatible object storage to encrypt/decrypt data in cloud, on-prem, edge, or offline environments. Available from AWS Marketplace.
No keys to store, manage, lose, or steal.

No human has to deal with encryption keys — ever. Keys are ephemeral. They exist only for the microseconds they're needed, then they're gone. No room for errors that end in downtime or audit findings.
Stolen data is genuinely unusable.

Protection is quantum-resistant and enforced architecturally, not by policies or credentials alone. If storage is breached, attackers get nothing usable. Authorized users continue working seamlessly.
Encryption needs to last. Keys don't.
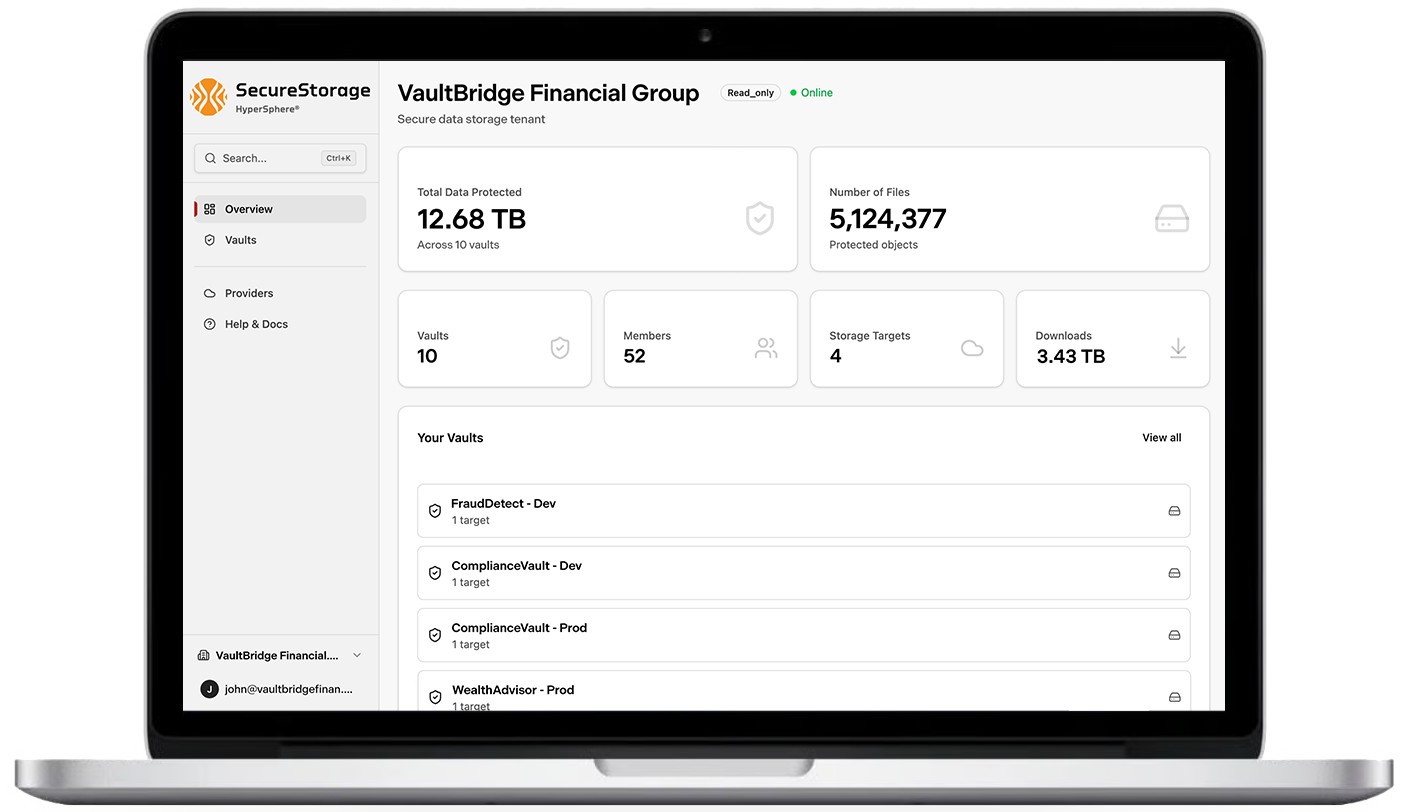
SecureStorage™ seamlessly encrypts data before it's written to storage and as users work. Deploys in hours with zero code changes. Quantum-resistance and ephemeral keys mean that even if storage is breached, data stays protected.
Wherever encryption keys persist, there's exposure.
Traditional KMS automates a lot. But it also centralizes key custody and stores a root key. Keys are targets. A compromised root key or privileged credential exposes everything encrypted under it.
89% of breaches involve valid credentials.
Attackers don't break encryption — they steal the keys. Stolen credentials, insider access, or a compromised root key exposes everything encrypted under it — instantly and completely. (IBM Cost of a Data Breach Report 2024)
"Harvest Now, Decrypt Later" is happening.
Adversaries are exfiltrating your encrypted data today, betting that quantum computing will crack the keys tomorrow. Every month of persistent keys is another month of compounding exposure.
Complex systems create the conditions for human error.
Key ceremonies, rotation schedules, IAM policies, access reviews — every manual process is a failure waiting to happen. Misconfigured permissions, stale keys, undocumented changes. The more moving parts in your KMS, the more ways it can go wrong.
What your team gets back immediately.
Engineering time reclaimed to focus on security and development.
Your security and DevSecOps teams can focus on actual threats — and stop wasting time on key management, rotation, and remediation.
Key management costs, complexities, and bottlenecks eliminated.
No KMS API call costs. No latency for users to complain about. No IAM clutter. No superfluous infrastructure to maintain. Just savings from day one.
Post-Quantum Cryptography (PQC) migration project postponed — indefinitely.
AES-256-GCM and KMAC256 today. No public-key crypto in the data path. No years-long migration required. Ready when quantum arrives.
Better than the alternatives.
Every alternative still leaves keys somewhere they can be found. HyperSphere doesn't.
AWS KMS, Azure Key Vault, HashiCorp Vault
- Root key persists — a single point of catastrophic failure
- Per-operation API calls add cost and latency at scale
- Privileged credential compromise exposes everything encrypted under it
- Key rotation requires scheduling, coordination, and downtime risk
Calamu, Myota, ShardSecure
- Still rely on traditional key management for decryption and reassembly
- Keys exist and can be stolen — there's still a key store to breach
- Fragmentation is a resilience strategy, not a cryptographic enforcement model
- No key hierarchy isolation — distribution and encryption are separate concerns
Encryption + distribution + ephemeral keying — all automated
- Keys derived in memory, destroyed after use — never stored on disk
- AES-256-GCM encryption on every frame — not just fragmentation
- Stolen ciphertext from any single backend is genuinely useless
- Key "rotation" is automatic, zero-downtime, built into the architecture
Validated by organizations that don't take chances.


Gartner
8× recognition by leading industry analyst for our unique approach to data protection.


NIST-Listed
The first cyberstorage product with a US government security baseline.


Cubic DTECH
Deployed in DoD tactical edge platforms where managing keys isn't operationally possible.


Forward Edge-AI
Bringing HyperSphere SecureStorage™ to distributed AI infrastructure.
Ready to eliminate key management overhead?
Get a live walkthrough of SecureStorage™ with a HyperSphere engineer. We'll show you exactly how zero-management encryption works — and what it eliminates from your stack.